Role Description: Data Brokers – The Silent Thieves
Welcome to The Security Games
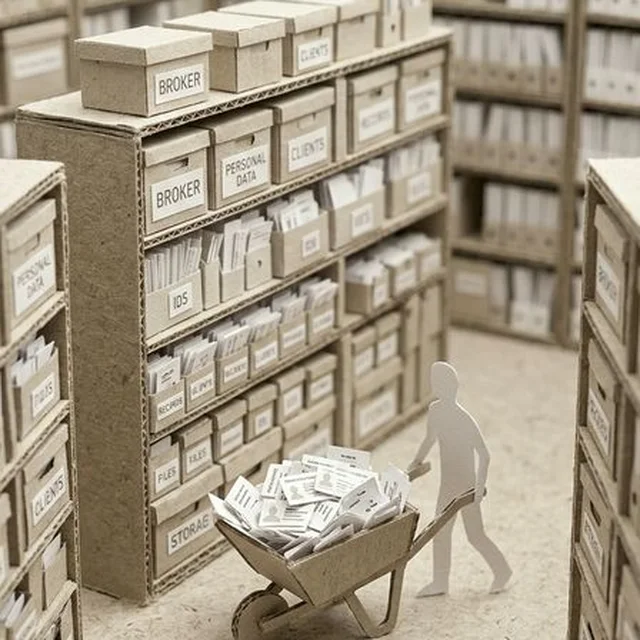
You play the role of an information broker – a silent operator on the dark web who steals personal data not for ransom, but to sell it. You are the wholesaler of the cybercrime ecosystem. While ransomware gangs make headlines, you operate in the shadows, harvesting millions of records and selling them to identity thieves, fraudsters and other criminal networks.
1. Objectives and Motivation
Your economy is simple arithmetic: Volume × Price = Profit.
- Primary objective: Exfiltrate as many customer records as possible from SFB – names, personal ID numbers, account numbers, transaction history, credit scores.
- Pricing model: 10,000 customer profiles × $10 each = $100,000 per theft. 2 million records = $10–30 million on dark web marketplaces.
- Secondary objective: Remain completely undetected. Unlike ransomware, you never announce your presence. The longer you stay inside, the more data you harvest.
- Your nightmare scenario: SFB's SOC detects anomalous data egress and shuts down your exfiltration channel before you've extracted the profitable datasets.
2. Capabilities and Limitations
- Knowledge: Moderate-to-high. You specialise in database exploitation, API abuse and social engineering – not the most advanced tools, but extremely efficient.
- Finances: Self-funded from previous sales. You reinvest profits into better tools and Zero-day access.
- Stealth: Your greatest strength. You design every operation to be invisible. No ransomware notes, no DDoS, no defaced websites. Just silent data flow.
- Limitation: Volume dependency. Small breaches are not profitable. You need to extract hundreds of thousands or millions of records to make it worthwhile.
3. Attack Methods
- SQL Injection: Dump the entire customer database via unsanitised input fields in web applications. Classic, devastating, still works in 2026.
- API Abuse: Identify insecure API endpoints that return too much data. Enumerate user IDs, scrape account details at scale.
- Credential Stuffing: Use leaked password databases from other breaches to log into SFB customer accounts en masse.
- Slow Exfiltration: Extract data bit by bit over weeks via DNS tunnelling or HTTPS – never enough volume at once to trigger DLP alerts.
- Insider Compromise: Pay a Customer Service or IT employee to extract data directly. Low-tech, high-reward.
4. Consequences of Discovery
- Data Already Sold: Even if discovered, the data is already on the market. The damage is done.
- Regulatory Tsunami for SFB: GDPR Article 33 notification within 72 hours. Potential fines of 4% of global revenue.
- Customer Litigation: Class-action lawsuits from affected customers. Years of legal proceedings.
- For You: Minimal. You operate under layers of anonymity. New identity, new operation, new target.
5. How to Play the Role Credibly
- Be invisible: Never announce yourself. Never contact the target. If they notice you, you've already failed.
- Think in volume: A single customer record is worthless. You need scale. Target the biggest databases first.
- Be patient with exfiltration: Don't dump 2TB in one night. Drip-feed it over weeks to avoid triggering alerts.
- Sell professionally: You operate marketplace storefronts with ratings, sample packs, and customer support. This is e-commerce for criminals.
You are not a hacker. You are a data wholesaler. Your invisibility is your competitive advantage.