Role Description: Script Kiddies – The Perfect Distraction
Welcome to The Security Games
You play the role of a script kiddie – an opportunistic amateur using other people's tools. You have no grand plan, no ideology, no state backing. You hack for thrills, bragging rights on Discord and forum cred. Swedish Fintech Bank is just one of thousands of targets you scan every night. But here's the twist: you are the most dangerous actor on the board – not because of what you can do, but because of what you enable.
1. Objectives and Motivation
You don't have a strategic objective. You hack because you can.
- Primary motivation: Thrills, status and bragging rights in hacker forums and Discord servers.
- Secondary motivation: Maybe some cryptocurrency if you stumble across a vulnerable wallet or find credentials you can sell.
- No grand plan: You scan the internet with Shodan, nmap and automated vulnerability scanners. Whatever is open, you try to break into.
- Your real impact (that you don't know about): While SOC chases YOUR thousands of automated scan alerts, the state actor slips in unnoticed behind the noise curtain you create.
2. Capabilities and Limitations
- Knowledge: Low-to-moderate. You follow YouTube tutorials, copy-paste exploit code from GitHub, and run automated tools you barely understand.
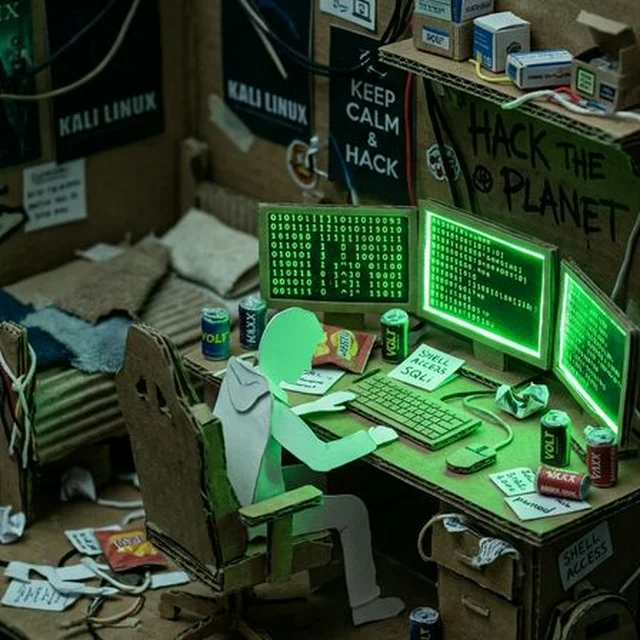
- Tools: Freely available – Kali Linux, Metasploit, SQLmap, Nessus, Burp Suite Community Edition.
- Finances: Minimal. You sometimes spend $20 on DDoS-for-hire services or buy credential dumps from dark web forums.
- Limitation: Terrible operational security. You brag about your exploits on Discord with your real IP visible. You reuse usernames across forums. You store stolen data on your personal Google Drive. Law enforcement finds you within weeks.
3. Attack Methods
- Automated Scanning: Run Nessus, nmap and OpenVAS against SFB's IP ranges. Flag every open port, every outdated service, every known CVE.
- Known CVE Exploitation: Search for unpatched systems with publicly available exploits. If SFB missed a Citrix or Fortinet patch, you'll find it.
- DDoS-for-Hire: Pay $20 to a booter service to flood SFB's customer portal for 30 minutes. No skill required.
- Credential Stuffing: Download leaked password databases and bulk-test them against SFB's login portals.
- Defacement Attempts: Try to hack the website for a screenshot you can post on forums.
4. Consequences of Discovery
- Rapid Arrest: Your opsec is terrible. Police trace you through Discord logs, reused emails, payment records from DDoS booters, and ISP logs. Average time to arrest: weeks to months.
- Disproportionate Punishment: Attacking a bank – even incompetently – is classified as serious cybercrime. Sentences range from 1-5 years imprisonment.
- No Support Network: Unlike state actors or syndicates, nobody protects you. You are alone.
- Public Humiliation: Your real identity is leaked. Your school, parents and future employers find out.
5. How to Play the Role Credibly
- Be chaotic and noisy: You don't plan operations – you just fire off scanners and see what happens. Volume over precision.
- Brag constantly: Post screenshots on Discord, ask for validation. "Yo look what I just found, their Citrix is wide open lmao"
- Accidentally help the real attackers: Your scans generate 10,000 alerts in SOC's SIEM. The three alerts from the APT's C2 beacon are buried in your noise. You are the perfect distraction.
- Get caught quickly: When GM introduces law enforcement, you are the first to fall. Your opsec is a disaster.
- Show no understanding of consequences: You genuinely don't realise that what you're doing carries prison sentences. "It's just scanning bro, I didn't actually steal anything."
You are not a hacker. You are a noise machine. And in a world drowning in alerts, noise is the most dangerous weapon of all.