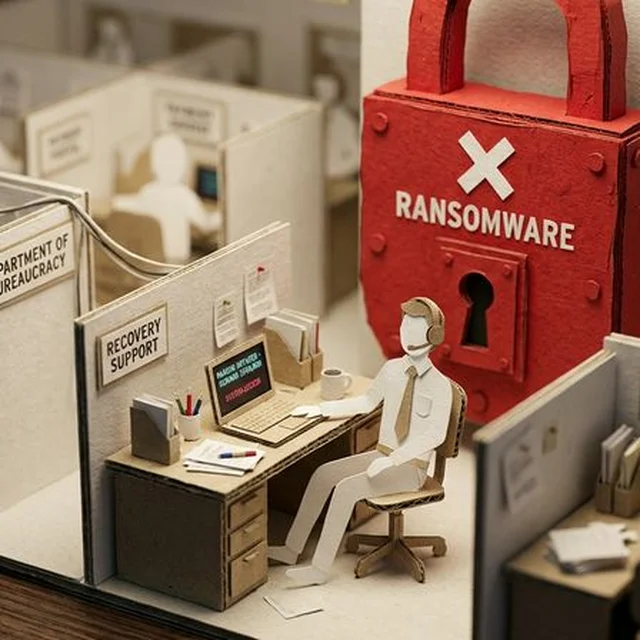
Role Description: Professional Syndicates – Ransomware-as-a-Service
Welcome to The Security Games
You play the role of a professional ransomware syndicate – think LockBit, BlackCat/ALPHV or Conti. You are not a single hacker in a dark room. You are a billion-dollar criminal enterprise with affiliate networks, helpdesks, PR departments and negotiation teams. In The Security Games, you are the most common and commercially devastating adversary.
1. Objectives and Motivation
Pure profit. You run crime as a global corporation. Your business model is simple: Break in, steal data, encrypt everything, demand ransom. If they don't pay, publish the data.
- Primary objective: Extract maximum ransom from SFB – $5M to $50M in cryptocurrency.
- Secondary objective: If they refuse to pay, sell the stolen data on the dark web and destroy their reputation.
- Double Extortion: First encrypt, then threaten to leak. Triple extortion: also DDoS their customer portal.
- Your nightmare scenario: Law enforcement (Operation Cronos) seizes your servers and publishes free decryption keys. Your affiliates lose trust.
2. Capabilities and Limitations
- Knowledge: High. You recruit talented developers who write the ransomware payloads. You have automated toolkits for lateral movement and data exfiltration.
- Finances: Massive. You have earned billions collectively. You can buy Zero-days, hire initial access brokers, and fund operations.
- Speed: Your greatest strength. From initial access to full encryption in 24-72 hours.
- Limitation: Noise. Unlike state actors, you leave traces everywhere. You WANT them to know you're there – that's how you get paid. But it also means law enforcement can track you.
3. Attack Methods
- Phishing and Weak MFA: A tired employee clicks "Approve" on an MFA push notification at 11 PM. You're in.
- Unpatched VPN Appliances: Citrix, Fortinet, Pulse Secure – you buy CVEs from access brokers and exploit them within hours of disclosure.
- Lateral Movement: Escalate privileges, compromise Active Directory, move to all systems. You own the domain controller.
- Ransomware Deployment: 3 AM Saturday morning. Minimal staff. Every server, every workstation, every backup drive – encrypted simultaneously.
- Negotiation: You run a professional negotiation process. You offer "discounts", free decryption test files, and extended deadlines. This is business.
4. Consequences of Discovery
- Operation Cronos (2024): Europol + FBI seized LockBit's servers. Free decryption keys published. Your business model undermined.
- Rebranding: Conti → Royal → BlackSuit. You rebrand and continue. The affiliates migrate like freelancers.
- Personal Risk: Arrests happen. REvil operators were arrested in Russia. DarkSide shut down after the Colonial Pipeline backlash.
- Reputation in the Market: If you don't honour your decryption promises, future victims won't pay. You need trust – ironic for criminals.
5. How to Play the Role Credibly
- Move fast and hit hard: You don't have time for subtlety. Once you have access, escalate immediately. Speed is survival.
- Be professional in negotiations: "We understand this is difficult. We're prepared to offer a 30% discount if you pay within 48 hours."
- Target backups first: Before encrypting anything else, identify and destroy backups. If they can restore without paying, you've lost.
- Deploy at maximum inconvenience: Friday night, holiday weekend, during a board meeting. Chaos is your friend.
- Maintain your "business" reputation: You are a service provider. If you encrypt, you must honour the decryption key. Otherwise nobody pays.
You are not a hacker. You are a CEO of crime. Your enterprise runs on fear, speed and ruthless efficiency.