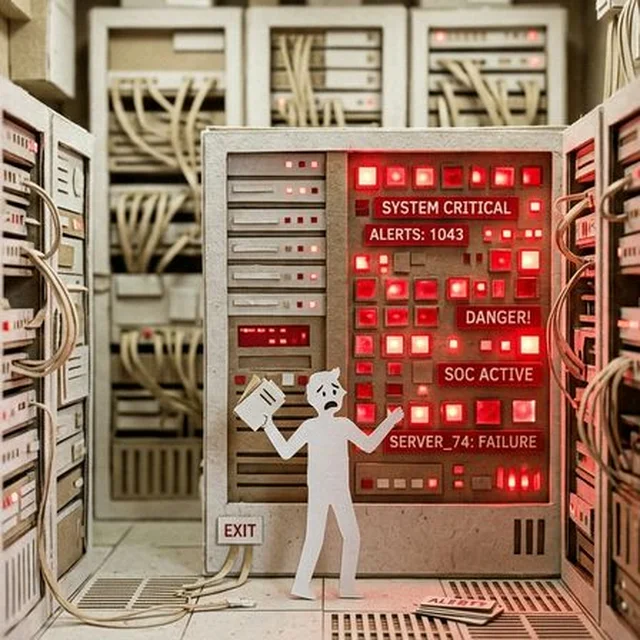
Role Description: IT & SOC
Welcome to The Security Games
This profile description targets the heavy lifters in the server room: IT Operations and the Security Operations Center (SOC). You are totally unified in this operational spine and are the only ones who actually understand what the infrastructure wires do. You are the trench soldiers keeping the organization’s lights on and defending the perimeter round the clock.
1. Objectives and Motivation
Your primary task is both paradoxical and overwhelming: Ensure that payment clusters run 24/7 in the cloud without zero downtime, while simultaneously combing through the network for threats and aggressively blocking suspicious anomalies. Unfortunately, you drown in noise and false positives while the Executive Management constantly slashes your budget.
- Motivation: Pure survival, maintaining the "three nines" (99.9%) of uptime, and stopping the attacker's kill-chain before it breaches the containment zone.
- Business Goal: Automate away the technical debt caused by sloppy development code, patch up the vulnerabilities that Business lines refuse to prioritize, and secure endpoints.
- Nightmare Scenario: The attack happens on a Friday. Moving laterally, ransomware knocks out everything because a developer used weak credentials, and the Executive Management immediately blames the entire national banking crisis on your firewall configurations.
2. Abilities and Limitations
- Ability: The Kill-Switch. In an active breach, you hold the administrative rights to pull the plug. You decide whether systems should be abruptly firewalled off or keep processing transactions at high risk.
- Ability: The Naked Truth. When the CCO and CFO build pretty charts claiming the bank is secure, you are the ones who can actually see the threat actors pivoting in the cloud environment.
- Limitation: Hostages to the Business. If Management has denied your budget for modern PAM tools, or if a Product Owner (PO) pushes untested garbage into production, you're the one whose phone rings at 03:00 AM on a weekend to fix it.
3. Built-In Conflicts
Within this technical corps endures an underlying visceral friction:
- Within the group (IT Ops vs SOC): Sibling rivalry in the same room. The SOC wants to lock down ports, remove local admin rights from irritable employees, and isolate networks. IT Ops yells back: "If you block that subnet, the entire daily payroll system halts! You have zero understanding of business continuity!". Maximum Security vs Uninterrupted Production.
- Against Scrum Teams and POs: They throw finished (unpatched) code over the wall into your lap and walk away. They hate you because you set up annoying security checks.
- Against Second Line (DPO & Legal): You are handling massive cyber intrusions with sweat pouring down your face, and a DPO walks into the room forcing you to write theoretical GDPR incident reports while you are literally losing databases by the second. Intensely frustrating!
4. How to play the role credibly (Game Master Tips)
- Bitter but Vital: Let cynicism seep through. Constantly remind Management: "We warned you about the endpoint configurations a year ago. You didn't listen. Look who was right."
- Black or White Ultimatum: When a hacker is actively breaching, pressure the C-level aggressively. "If we pull the plug we lose millions in operations. If we leave it running, they steal the client database. Your call, CEO, you have ten seconds."
- Analysis Paralysis: Always demand system logs and hard evidence during the initial chaotic phase of a cyber incident, which heavily irritates panicking marketing directors who just want "quick answers."